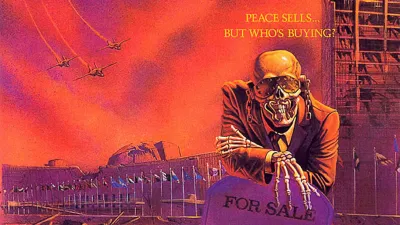
They Live...
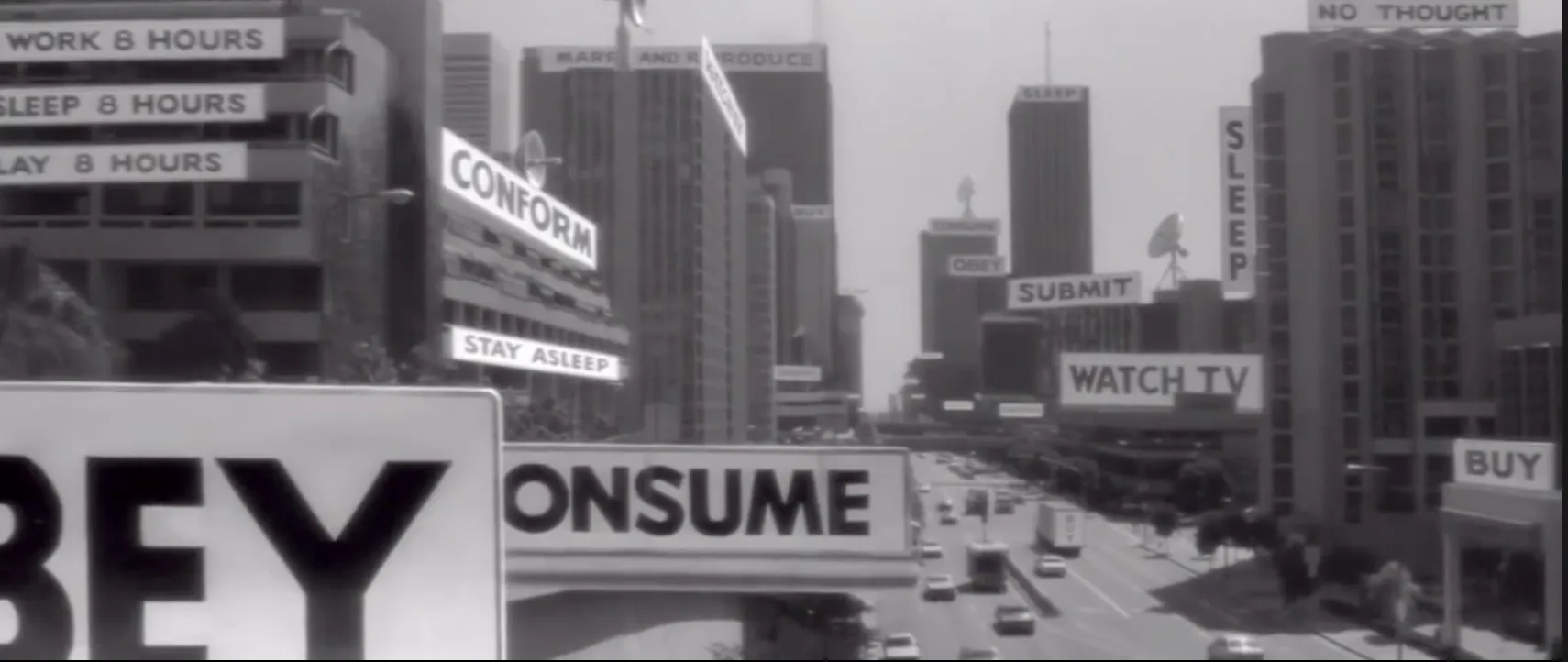
...we sleep
January 2026. A consulting firm publishes its annual CISO radar. 150 topics arranged in concentric circles: emerging, trending, mature. Six domains: Protect, Detect & Respond, Identity & Trust Services, Risk & Governance, Compliance & Privacy, Operational Resilience.
It's a beautiful object. Colorful, comprehensive, professional. CISOs download it, present it to their boards, use it to prioritize investments.
I put on the glasses. I counted. I looked for data. And I understood: it doesn't work.
Ten items, 150 on the radar
Let's take ten items at random from the 2026 radar.
Zero Trust Access, classified as "mature," supposedly already addressed. An analysis of 156 enterprise deployments shows a range of $180,000 to $4.2 million depending on complexity, over 12 to 18 months¹. An in-house 24/7 SOC costs between $1.5 and $5 million per year². SASE, XDR, IAM for OT, Post Quantum Crypto roadmap, DORA compliance, AI red teaming, Cyber vault, Digital dependencies mapping: each requires FTEs, budget, time. None is free.
Ten items. Realistic range: $5 to $15 million over three years, 20 to 50 cumulative FTEs.
The radar lists 150.
6.4% of the IT budget
The same firm that publishes the radar measures enterprise cyber maturity annually³.
Large French companies allocate an average of 6.4% of their IT budget to cybersecurity, at the low end of the recommended range. They have one cyber expert per 1,016 employees. Top performers in the financial sector reach 1 per 80.
Intentions to increase cyber budgets dropped 15 points in one year⁴. Headcount intentions dropped 13 points. For SMEs, 75% spend less than €2,000 per year on cybersecurity⁵.
A Fortune 500 company allocates $50 to $150 million to cybersecurity. Teams of 100 to 300 people. That's substantial. Put that against 150 items.
The math doesn't work, anywhere, even for the biggest players.
I'm not saying the radar is wrong. It describes a world where resources are unlimited. That world doesn't exist.
Everyone on the same path
In practice, organizations position themselves on the radar according to their means. This is what I observe in the field.
Large enterprises work on "emerging" topics. They have budgets to experiment, teams to absorb complexity, media presence to communicate their lead.
Mid-sized companies follow "trending" topics. They wait for solutions to stabilize, prices to drop, skills to spread.
SMEs arrive at "mature" topics. When it's become standard, packaged, accessible.
Everyone follows the same path. The only variable is position on the path.
This is true in Paris. True in New York. True everywhere the Western cybersecurity management model applies. No one questions the path itself.
One map to learn
If all organizations implement the same building blocks in the same order, they converge toward the same architecture. Same tools, same configurations, same weaknesses.
For an attacker, this is considerable simplification. One map to learn. A vulnerability in a radar "leader" tool hits everyone simultaneously. A bypass that works somewhere works everywhere.
Collective "maturity" measured by radar alignment produces collective vulnerability. The more homogeneous the herd, the faster the epidemic spreads.
I've documented elsewhere the mathematical imbalance between offense and defense in the AI era. Defense homogenization makes it worse. The attacker has only one target to study. The defender has only one posture to hold.
Chicago, Frankfurt, same SOC
The radar isn't a European product imported from the United States. It's the GPS for the entire Western world. American CISOs follow Gartner. European CISOs follow Gartner and its local variants. Same categories, same acronyms, same logic. A SOC in Chicago looks like a SOC in Frankfurt.
The difference lies in what surrounds the radar.
In the United States and Israel, the cyber ecosystem operates in symbiosis: talent circulates between agencies and startups, offensive technologies become commercial products, intelligence feeds industry⁶. The radar fits into this loop. An American bank's CISO follows the radar. The NSA doesn't. Two logics coexist.
Europe imported the radar without the loop. It grafted it onto a closed circuit (public funding, certification, government contracts, stagnation) that produces neither global champions nor alternative capabilities⁷.
When the radar is no longer enough, when the imbalance between offense and defense becomes unmanageable, America has a Plan B. Europe doesn't.
The blind spots
I looked in the 2026 radar for certain topics I've documented elsewhere.
Technical debt is absent. Legacy systems that can't be patched, critical business applications running on obsolete OSes, industrial protocols from another age. Nothing.
Budget trade-offs aren't there. How to choose between Zero Trust and SOC when you can't do both. How to explicitly give up on certain topics. Silence.
Geopolitical dependency on American vendors leaves no trace. Neither does the growing imbalance between offense and defense: the radar lists "AI for security" on the defense side and "AI red teaming" on the test side, but not the fundamental question.
Deep organizational resilience is also missing. Not backup tools, not packaged continuity plans. The ability to operate in degraded mode, to decide under pressure, to rebuild without systems.
What doesn't appear on the radar doesn't exist in strategic conversation. What doesn't exist in conversation doesn't receive budget. In New York as in Paris.
Why it persists
150 impossible items to address. Stratification that puts everyone on the same track. Homogenization that creates collective vulnerabilities. Deep blind spots on real risks.
The system runs. Radars come out, presentations get made, budgets align. Yet its real function is not to ensure our security.
What remains is understanding why it persists.
What I don't know
I'm not claiming the firms producing these radars act in bad faith. Producing a comprehensive inventory meets a demand. CISOs want a complete map. Firms provide it.
I also don't know if an alternative exists. A radar that said "here are 10 topics, ignore the rest" would lose in comprehensiveness what it gained in realism. Firms that tried would risk being judged incomplete compared to competitors.
The system perhaps perpetuates itself because it suits everyone. Except those who must implement it.
This article is part of a series analysing the structural flaws of Western cybersecurity (articles 1-5 in French):
- Article 1 : La vulnérabilité de la gestion des vulnérabilités
- Article 2 : La dépendance européenne aux standards américains
- Article 3 : Les États, architectes cachés du marché noir des vulnérabilités
- Article 4 : L'IA ou l'effondrement du modèle défensif occidental
- Article 5 : Desert Power — survivre sans l'Empire
- Article 6: I Am Altering the Deal
- Article 7: The Last Channel
- Article 8: Lord of Cyber War
- Article 9: The digital hawks
References
¹ Axis Intelligence (2025). "Zero Trust Implementation Cost Calculator 2025: Enterprise Budget Planning Tools" — Analysis of 156 enterprise deployments. https://axis-intelligence.com/zero-trust-implementation-cost-calculator-2025/
² Netsurion (2023). "The True Cost of Setting Up and Operating a 24x7 Security Operations Center"; Lumifi (2024). "What Does It Cost to Build a Security Operations Center?"; Ponemon Institute — Average $2.86M/year for internal SOC.
³ Wavestone (2025). "Cyber Benchmark 2025" — 6.4% of IT budget, 1 expert per 1,016 employees. https://www.wavestone.com/fr/insight/cyber-benchmark-2025/
⁴ CESIN / OpinionWay (2025). "10th annual cybersecurity barometer" — Budget intentions -15 points, headcount -13 points. https://cesin.fr/
⁵ Cybermalveillance.gouv.fr (2025). "2nd national SME cyber maturity barometer" — 75% of SMEs: cyber budget < €2,000. https://www.cybermalveillance.gouv.fr/
⁶ Atlantic Council (2024). "Sleight of Hand: How China Weaponizes Software Vulnerabilities" — Documentation of US offensive ecosystem.
⁷ Franck Rouxel (2025). "We are the champions... or not" — Analysis of the French cyber startup ecosystem: nearly 150 vendors, over one billion euros raised, zero independent global leader.