The Sting

Five-story sovereignty, zero-floor control
On February 5, 2026, at Bercy, three ministers unveil a Prime Minister's circular on government digital procurement¹. Sovereignty becomes the top criterion, ahead of performance, security and cost. The same day, the government abandons the Health Data Hub's interim solution and launches migration to a SecNumCloud-qualified cloud via the UGAP "Nuage Public" framework. Six years after the first promise.
Nine days later, at the Munich Security Conference, U.S. Secretary of State Rubio calls the postwar order "a dangerous delusion" and denounces the outsourcing of sovereignty to multilateral institutions². In the same speech, he declares that the United States and Europe "belong together" and receives a standing ovation. The preceding five months set the stage. On September 5, 2025, the Commission fines Google €2.95 billion for abuse of dominance in adtech³. Trump threatens the same day to launch a Section 301 investigation to "reverse the unfair penalties." On December 5, the first Digital Services Act fine: €120 million against X for its deceptive verification system and lack of advertising transparency⁴. On December 16, the USTR formalizes the threat: the EU is pursuing "a discriminatory series of lawsuits, taxes, fines, and directives against American service providers⁵."
On December 23, Rubio revokes the U.S. visa of Thierry Breton and four others, labeled "figures in the global censorship industrial complex⁶." An individual sanction for enforcing a European law. On February 3, 2026, the House Judiciary Committee publishes a 160-page report and the full Commission decision against X, obtained by subpoena, calling it a "censorship order⁷."
Between these events: the implementing decree for Article 31 of the SREN Act, due since November 2024, remains missing⁸. The February 5 circular references an unpublished vademecum that relies on this unenforceable article. Each announced text references a text that does not exist.
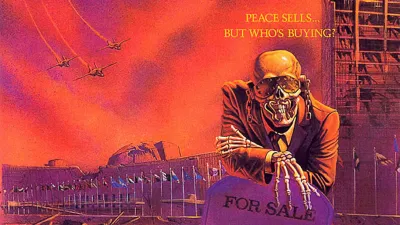
The tower
European digital sovereignty is a five-story building. The February 5 circular acts on a single floor. The other four appear in no French or European text currently in force.
Floor 1 — Who detects the flaws
Europe's capacity to know whether a system is vulnerable depends on the American National Vulnerability Database. 85% of security solutions deployed in Europe rely on its data⁹. The NVD has accumulated 26,628 unanalyzed CVEs since February 2024¹⁰. NIST has publicly admitted it is "fighting a losing battle" and announced it would prioritize rather than comprehensively enrich¹¹. CISA's KEV, the only federal indicator of active exploitation, covers 0.5% of published CVEs¹². It requires a CVE identifier for each entry.
The European EUVD has existed since 2024. Its budget: €24 million over three years¹³. The NVD operated on an annual budget ten times larger for twenty years. And it is collapsing anyway.
Floor 2 — Who hosts the data
65% of the European public cloud market is controlled by three American companies: AWS, Azure and Google Cloud. European providers hold 15% of the market¹⁴. In France: €25 billion cloud market, 80% with these three providers¹⁵. UGAP announces eighteen SecNumCloud-qualified offerings. Five actually are at the time of announcement¹⁶. The ANSSI director general stated in January 2026 that SecNumCloud is "a cybersecurity tool, not an industrial policy instrument¹⁷."
The circular places sovereignty as the top criterion and relies on SecNumCloud as the primary response. It provides no instrument for the dimensions SecNumCloud does not cover: technology substitution, control of software components, long-term dependency reduction.
Floor 3 — Which law applies
The CLOUD Act allows U.S. authorities to demand access to data hosted by companies subject to American law, regardless of where the data is stored. SecNumCloud reduces this risk through legal isolation. But the decree making this protection mandatory for sensitive data does not exist. Article 31 of the SREN Act requires it. The Council of State is reviewing it. The Senate committee recommended its publication "as soon as possible¹⁸." Eighteen months past the legal deadline, nothing.
Between the national level and CADA sits the EUCS, the European cloud certification scheme. Under discussion since December 2020, it was meant to harmonize security requirements across the EU. Five years later, only one European certification scheme has been adopted (the EUCC for ICT products, in 2024). The EUCS remains blocked.
The Cybersecurity Act only allows ENISA to set technical criteria. Brussels considers immunity to extraterritorial laws a political requirement, not a technical one. The sovereignty criteria, the "High+" level, functional equivalent of SecNumCloud, were removed from the draft in 2024 under pressure from U.S. industry and several Member States.
The Commission proposed on January 20, 2026 a revision of the Cybersecurity Act (CSA2) to allow consideration of "non-technical risk factors"¹⁹ᵇⁱˢ. Its official Q&A admits it: the EUCS needs both the revised CSA and CADA to integrate sovereignty aspects. Three unfinalized texts, in a dependency chain.
The European CADA (Cloud and AI Development Act), expected in Q1 2026, is to establish EU-wide cloud eligibility requirements¹⁹. Two options: ownership criteria (direct escalation with Washington) or a risk-based assurance model (opening the door to hyperscaler "sovereign" offerings). The choice has not been made. If CADA opts for assurance, it could render obsolete certain provisions of the SREN decree, the decree that still does not exist.
Floor 4 — Who builds the tools
GitHub (Microsoft) hosts development. npm (Microsoft) distributes packages. openDesk, the flagship of European software sovereignty led by Germany's ZenDiS, depends 72% on components maintained by American developers²⁰. 40% of npm packages depend on a single maintainer²¹.
In December 2025, Senator Cotton asked the National Cyber Director to develop federal capability for tracking the national origin of open-source contributors²². The Hegseth memorandum orders the Department of Defense to "purge its software of any Chinese involvement²³." In August 2025, Hunted Labs revealed that a developer based at Yandex was the sole maintainer of fast-glob, a package integrated into more than thirty DoD projects, downloaded 81 million times per week²⁴.
Europe promotes open source as a path to autonomy. The United States, having dominated this ecosystem, is beginning to treat it as an infiltration vector to be monitored and purged.
Floor 5 — Who defines how AIs communicate
MCP (Anthropic) and A2A (Google) define the communication protocols between AI agents and between agents and tools. In December 2025, MCP was transferred to the Agentic AI Foundation (Linux Foundation): 97 million monthly SDK downloads²⁵. In June 2025, A2A was transferred to a separate Linux Foundation project, backed by over 150 organizations²⁶.
The Governing Boards of both structures count exclusively American Big Tech among their founding Platinum members: Anthropic, OpenAI, Google, Microsoft, AWS, Salesforce, ServiceNow, Cisco²⁷. No European actor at the governance table. NIS2 and the Cyber Resilience Act impose security requirements on software components. No European text addresses inter-agent AI coordination protocols.
If agentic AI becomes the dominant mode of automation (and industrial signals converge in that direction), controlling the communication protocols between agents amounts to controlling the internal operations of the organizations that deploy them.
The scissors
I read the Munich-Bercy-Omnibus sequence as a convergent movement. Other readings are possible.
On the American side: Cotton demands nationality-based open-source purges. Hegseth orders DoD software purges. The USTR arms Section 301 against the EU. The visa ban sanctions enforcement of the DSA. The House Judiciary Committee labels European regulation "censorship." The United States closes its supply chain flank and opens a commercial front against European regulation.
On the European side: the Commission published on November 19, 2025 the Omnibus, a package that loosens the GDPR through a fast-track procedure bypassing impact assessment²⁸. Among the changes: the subjective redefinition of personal data (the GDPR would cease to apply if a company declares it does not intend to identify individuals), authorization to train AI on personal data via "legitimate interest" without consent, restriction of sensitive data to data identifying "directly" a protected characteristic²⁹. These relaxations benefit American hyperscalers and European companies alike.
In 2025, the Commission fined Apple €500 million and Meta €200 million (DMA, April 23)³⁰, Google €2.95 billion (antitrust, September 5)³, and X €120 million (DSA, December 5)⁴. The same Commission loosens through the Omnibus the data protection framework those fines purport to defend.
The contradiction is probably not intentional. Different Directorates-General pursue different objectives. DG Competition fines. DG Connect regulates platforms. DG Grow pushes competitiveness. Nobody is watching the whole picture.
The United States protect their components. Europe deprotects its data. The technical dependencies remain intact at every floor of the tower.
The cost of the unfinished sentence
€4.5 billion in annual government digital procurement, with no operational sovereignty benchmark³¹. €1.2 to 1.5 billion to replicate CVE/NVD functions alone⁹. The Munich Security Report puts "€3 to 5 trillion" to replace American technologies². Without source, without breakdown, without methodology.
The relevant cost is that of compounding inaction. Each year without the Article 31 decree, public procurement renews dependencies by default. Each year without a seat on the MCP/A2A Governing Boards, one more specification is adopted without European influence. Each year of underfunded NVD, the backlog of unanalyzed CVEs extends the blind spot. Europe has no operational database capable of taking over.
What I do not know
Whether CADA will opt for ownership or assurance criteria. Whether the Cybersecurity Act revision will effectively integrate the "non-technical risk factors" that would allow the EUCS to include sovereignty criteria, after five years of blockage. Whether Section 301 will be formally launched or maintained as a threat. Whether the Omnibus will be amended in Parliament (the S&D, Renew and Greens groups have expressed reservations²⁹). Whether the Article 31 decree will come out in Q1 2026 as announced, and in what version.
What I know
Europe is building a digital sovereignty whose vulnerability detection, legal infrastructure, development tools and AI orchestration protocols are under American governance. The February 5 circular certifies the box. No text in force certifies the ability to know whether what is inside is safe.
The government wrote the standard, announced the doctrine, passed the law, then turned the page without finishing the sentence. This observation is not a matter of interpretation. Article 31 SREN, its missing decree, the circular that cites it, the vademecum that extends it: these are public documents. Their state of completion is too.
The most likely scenario at twelve months (Munich Security Report, ~50%) is controlled escalation: Section 301 in investigation phase, DMA/DSA fines continuing, CADA published with assurance criteria, EUCS still awaiting the CSA revision, Omnibus amended². Tension maintained, no rupture. This is the most comfortable scenario, and the most dangerous. A system under constant tension that never breaks never triggers the overhaul. Dependencies persist, debts accumulate, and compound interest does the rest.
This special edition covers topics addressed across all my analyses on digital sovereignty and cybersecurity, available at klaerenn.
References
¹ Press release, Ministry of the Economy and DINUM, February 5, 2026 https://presse.economie.gouv.fr/?p=170369 · https://www.numerique.gouv.fr/sinformer/espace-presse/achats-publics-num%C3%A9riques-letat-pr%C3%A9cise-sa-doctrine/
² Munich Security Conference (2026). Munich Security Report 2026 — Under Destruction; Rubio, M. (2026). Speech at MSC, February 14, 2026 (official transcript) https://securityconference.org/en/msr-2026/ · https://www.state.gov/releases/2026/02/secretary-of-state-marco-rubio-at-the-munich-security-conference/
³ European Commission (2025). Antitrust decision adtech, September 5, 2025 — €2.95 billion fine on Google for abuse of dominant position https://ec.europa.eu/commission/presscorner/detail/en/ip_25_4543 · CNBC, "EU slaps Google with $3.3 billion fine," September 5, 2025
⁴ European Commission (2025). First DSA decision, December 5, 2025 — €120 million fine on X https://ec.europa.eu/commission/presscorner/detail/en/ip_25_6470 · TechCrunch, "EU fines X $126M for DSA violations," December 5, 2025
⁵ U.S. Trade Representative (2025). Statement of December 16, 2025 — cited by Bloomberg, Fortune, TTNews. Presidential memorandum on digital services taxes: February 21, 2025 https://www.ttnews.com/articles/trump-eu-digital-tax · Skadden, "Presidential Memorandum on Digital Services Taxes"
⁶ CNBC (2025). "'Witch hunt': Ex-EU commissioner Breton denounces U.S. visa ban targeting 'censorship'," December 24, 2025 — Section 212(a)(3)(C) of the Immigration and Nationality Act https://www.cnbc.com/2025/12/24/witch-hunt-ex-eu-commissioner-breton-denounces-us-visa-ban.html · Euronews, "US visa ban EU officials," December 2025
⁷ U.S. House Judiciary Committee (2026). "Censoring Americans: How the EU Exports Censorship to the United States," 160 pages + full Commission decision obtained by subpoena, February 3, 2026 https://judiciary.house.gov/ · TechPolicy.Press, "A Misread of European Platform Regulation," February 3, 2026 · https://www.techpolicy.press/a-misread-of-european-platform-regulation/
⁸ Loi n° 2024-449, May 21, 2024 (SREN Act), Article 31 — Six-month deadline for implementing decree (Council of State) https://www.legifrance.gouv.fr/jorf/id/JORFTEXT000049563035
⁹ See article 2 in this series: "European dependence, hostage to a vulnerability system it does not control" https://www.klaerenn.fr/la-dependance-europeenne-otage-dun-systeme-de-vulnerabilites-quelle-ne-controle-pas/
¹⁰ Gamblin, J. (2026). "NVD Analysis Status" — 26,628 unanalyzed CVEs as of October 30, 2025 https://github.com/jgamblin/NVDAnalysisStatus
¹¹ Cybersecurity Dive (January 2026). "NIST is rethinking its role in analyzing software vulnerabilities" — quote: "We're fighting a losing battle" https://www.cybersecuritydive.com/news/nist-cve-vulnerability-analysis-nvd-review/810300/
¹² See article 7 in this series: "The Last Channel" https://www.klaerenn.fr/the-last-channel/
¹³ ENISA, EU Vulnerability Database (EUVD). Budget and roadmap https://www.enisa.europa.eu/topics/vulnerability-management
¹⁴ Synergy Research Group / IDC, European cloud market shares 2025. Referenced in Atlantic Council report, February 12, 2026 https://www.atlanticcouncil.org/in-depth-research-reports/report/digital-sovereignty-europes-declaration-of-independence/
¹⁵ Senate inquiry committee on public procurement, Wattebled-Uzenat report, July 8, 2025 https://www.senat.fr/travaux-parlementaires/structures-temporaires/commissions-denquete/commission-denquete-sur-les-couts-et-les-modalites-effectifs-de-la-commande-publique-et-la-mesure-de-leur-effet-dentrainement-sur-leconomie-francaise.html
¹⁶ nuagepublic.fr portal, UGAP "Nuage Public" FAQ; Vincent Strubel, "SecNumCloud en (pas si) bref," LinkedIn, January 6, 2026 https://www.nuagepublic.fr/faq
¹⁷ Strubel, V. (2026). Hearing before the Senate inquiry committee on public procurement, January 2026 https://www.senat.fr/travaux-parlementaires/structures-temporaires/commissions-denquete/
¹⁸ Senate inquiry committee, recommendation no. 22: "Publish the implementing decree for Article 31 of the SREN Act as soon as possible" https://www.senat.fr/travaux-parlementaires/structures-temporaires/commissions-denquete/commission-denquete-sur-les-couts-et-les-modalites-effectifs-de-la-commande-publique-et-la-mesure-de-leur-effet-dentrainement-sur-leconomie-francaise.html
¹⁹ CEPA (2026). "One Tech Policy Battle After Another," February 12, 2026; Politico EU, "Washington pushes back against EU's bid for tech autonomy," February 13, 2026 https://cepa.org/article/one-tech-policy-battle-after-another/ · https://www.politico.eu/article/eu-bid-for-tech-autonomy-washington-us-pushes-back/
¹⁹ᵇⁱˢ European Commission (2026). Proposal for revision of the Cybersecurity Act (CSA2), COM(2026) 11, January 20, 2026; Q&A: "On cloud, the new Cybersecurity Act complemented by the upcoming CADA will fill gaps related to sovereignty aspects and non-technical risks"; EU ISS, "Technical is political: When a cloud certification scheme divides Europe," November 3, 2025; CEP, "EU Cloud Certification at an Impasse," April 25, 2025 https://digital-strategy.ec.europa.eu/en/library/proposal-regulation-eu-cybersecurity-act · https://digital-strategy.ec.europa.eu/en/faqs/cybersecurity-package-questions-answers · https://www.iss.europa.eu/publications/briefs/technical-political-when-cloud-certification-scheme-divides-europe · https://www.cep.eu/eu-topics/details/eu-cloud-certification-at-an-impasse.html
²⁰ See "The blind spot of digital sovereignty: why open source will not save us" — npm dependency analysis of openDesk https://www.klaerenn.fr/langle-mort-de-la-souverainete-numerique-pourquoi-lopen-source-ne-nous-sauvera-pas/
²¹ Zimmermann et al. (2019). "Small World with High Risks: A Study of Security Threats in the npm Ecosystem." USENIX Security https://www.usenix.org/conference/usenixsecurity19/presentation/zimmerman
²² Cotton, T. (2025). Letter to National Cyber Director Sean Cairncross, December 17, 2025 https://www.cotton.senate.gov/news/press-releases/cotton-to-cairncross-address-national-cyber-security-risk
²³ Hegseth, P. (2025). "Enhancing Security Protocols for the Department of Defense," memorandum dated July 18, 2025 https://media.defense.gov/2025/Jul/22/2003759081/-1/-1/1/ENHANCING-SECURITY-PROTOCOLS-FOR-THE-DEPARTMENT-OF-DEFENSE.PDF
²⁴ Hunted Labs (2025). Report on fast-glob: sole maintainer based at Yandex, 81M+ downloads/week, 30+ DoD projects https://huntedlabs.com/popping-fast-globs-hood/
²⁵ Anthropic (2025). "Donating the Model Context Protocol and establishing of the Agentic AI Foundation," December 9, 2025; Linux Foundation, AAIF announcement, December 9, 2025 https://www.anthropic.com/news/donating-the-model-context-protocol-and-establishing-of-the-agentic-ai-foundation · https://www.linuxfoundation.org/press/linux-foundation-announces-the-formation-of-the-agentic-ai-foundation
²⁶ Linux Foundation (2025). "Linux Foundation Launches the Agent2Agent Protocol Project," Open Source Summit North America, June 23, 2025; Google Developers Blog, "Google Cloud donates A2A to Linux Foundation," June 23, 2025 https://www.linuxfoundation.org/press/linux-foundation-launches-the-agent2agent-protocol-project-to-enable-secure-intelligent-communication-between-ai-agents · https://developers.googleblog.com/en/google-cloud-donates-a2a-to-linux-foundation/
²⁷ AAIF Platinum members: Anthropic, Block, OpenAI (co-founders), AWS, Bloomberg, Cloudflare, Google, Microsoft. A2A Governing Board: AWS, Cisco, Google, Microsoft, Salesforce, SAP, ServiceNow. Sources: Linux Foundation announcements²⁵ ²⁶; Block, "Block, Anthropic, and OpenAI Launch the Agentic AI Foundation," Dec. 9, 2025 https://block.xyz/inside/block-anthropic-and-openai-launch-the-agentic-ai-foundation
²⁸ noyb (2025). "Digital Omnibus: EU Commission wants to wreck core GDPR principles," November 19, 2025 — fast-track procedure bypassing impact assessment and inter-service consultation https://noyb.eu/en/digital-omnibus-eu-commission-wants-wreck-core-gdpr-principles · https://www.techpolicy.press/why-the-eus-gdpr-simplification-reforms-could-unravel-hardwon-protections/
²⁹ IAPP (2025). "EU Digital Omnibus: Analysis of key changes," November 2025 — detail of GDPR modifications, parliamentary reactions https://iapp.org/news/a/eu-digital-omnibus-analysis-of-key-changes · White & Case, "GDPR Under Revision: Key Takeaways from Digital Omnibus Regulation Proposal," 2025
³⁰ European Commission (2025). First DMA fines: Apple €500M and Meta €200M, April 23, 2025 https://ec.europa.eu/commission/presscorner/detail/en/ip_25_1866 · Hunton Andrews Kurth, "European Commission Fines Apple and Meta for Non-Compliance with the DMA," April 2025 · PwC Legal, "Enforcement of the DMA — First fines on Apple and Meta," May 20, 2025
³¹ Cour des comptes (2025). Les enjeux de souveraineté des systèmes d'information civils de l'État, October 31, 2025 https://www.ccomptes.fr/fr/publications/les-enjeux-de-souverainete-des-systemes-dinformation-civils-de-letat