The Digital Hawks
When vulnerability becomes ammunition
A vulnerability is a flaw to fix. That's what the CVE/NVD ecosystem has been telling us since 1999. That's what compliance frameworks repeat. That's what most cybersecurity leaders believe.
In June 2025, the Atlantic Council published a report saying the opposite. A vulnerability is an asset to acquire, stockpile, exploit. And the United States doesn't have enough.
The reversal
The report is titled "Crash (exploit) and burn"¹. Thirty-six pages on America's "offensive cyber supply chain." The question posed: if the United States wants to use more of its offensive capabilities against China, does it have the necessary supply chain?
Translation: do they have enough exploitable vulnerabilities in stock?
The answer: no. The pipeline is dysfunctional. Too many intermediaries between the researcher who discovers a flaw and the agency that exploits it. Acquisition cycles of 6 to 18 months per exploit. Dependence on foreign talent. Prices exploding from $100,000 at the researcher level to $750,000 or a million at the end customer.
The recommendations follow: create accelerators at the Department of Defense, establish a government vulnerability broker, expand NSA offensive training programs.
I documented states as buyers on the vulnerability black market⁶. This report takes it further: it's now about industrializing the supply.
The word "defense" appears in the report. As an obstacle. Google and Apple's investments in cybersecurity "obstruct" American offensive capabilities, the author notes. When Microsoft patches a flaw, that's one exploit disappearing from available stock.
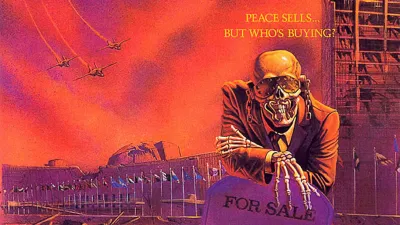
Two visions of vulnerability now coexist. One, inherited from the CVE model, sees the flaw as a collective risk to reduce. The other, carried by this report, sees the flaw as a strategic resource to capture before the adversary does.
These two visions are incompatible. And one is winning in Washington.
Who carries this vision
The Atlantic Council report isn't an intellectual accident. It's part of an ecosystem.
The Atlantic Council counts among its donors the Department of Defense, Raytheon Technologies, Lockheed Martin, Northrop Grumman². The Cyber Risk Wednesday program, which produces this type of analysis, is explicitly funded by Raytheon—the same Raytheon cited in the report as a key player in the pipeline to "secure."
The author declares her affiliations. Her husband runs the DARPA INGOTS program, mentioned in the recommendations as a model for automated exploit chain research.
I'm not suggesting a conspiracy. I'm describing an ecosystem where funders, analysts, and beneficiaries of the recommendations form a coherent circuit. The contractors fund the think tank. The think tank recommends increasing budgets. The budgets go to the contractors³.
This circuit produces a worldview where vulnerability is ammunition, not a defect. And this vision directly influences American policy.
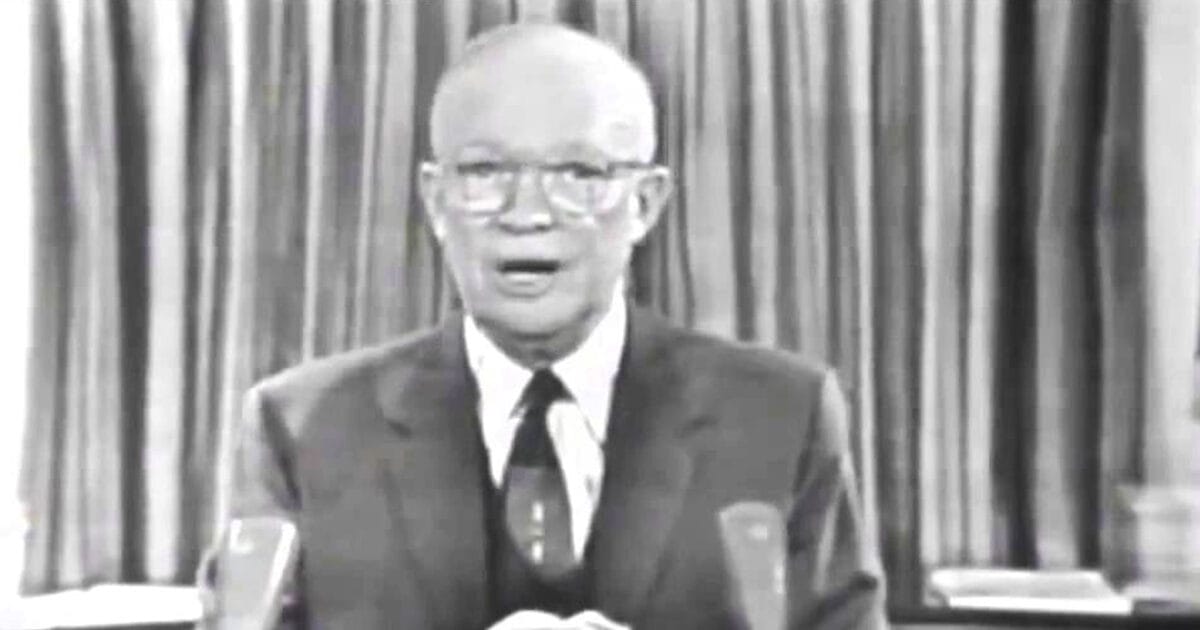
In August 2018, the Trump administration published National Security Presidential Memorandum 13, which lifted restrictions on offensive cyber operations. Result according to a Cyber Command official: more operations in a few months than in the previous ten years.
The Biden administration tried to revise this text. The Pentagon resisted. The essence remains.
The Atlantic Council report fits into this continuity. It doesn't question the offensive posture. It seeks to optimize it.
What China understood
While Washington debates optimizing its pipeline, Beijing solved the problem differently.
Since September 2021, the Regulation on Management of Security Vulnerabilities requires companies operating in China to report any discovered vulnerability to the government within 48 hours⁵. Before any fix. Before any publication.
The result is documented. The Chinese CNNVD database publishes vulnerabilities in an average of 13 days. The American NVD takes 33 days. China covers 75% of flaws within a week. The United States takes three to five weeks⁴.
China isn't trying to buy vulnerabilities on a market. It nationalized discovery. Every researcher, every tech company operating on its territory automatically feeds the government stockpile.
The two systems no longer speak the same language. One optimizes a market. The other abolished it.
The blind spot
The Atlantic Council report has a theory of victory: secure the offensive pipeline, capture vulnerabilities before the adversary, maintain the advantage.
It has no theory of escalation.
What happens when two powers stockpile vulnerabilities on each other's critical infrastructure? Volt Typhoon maintains dormant access on the American electrical grid. The United States probably has equivalent access. Each side prepares the capability to paralyze the other.
Who activates first? How do you distinguish a red line test from a declaration of war? Who de-escalates when systems on both sides react faster than humans can decide?
These questions are absent from the report. They are absent from the debate in Washington.
Between 1906 and 1914, the United Kingdom and Germany engaged in a battleship race. Each construction on one side justified a response from the other. The shipyards pushed for escalation. Each decision was rational at the individual actor level.
The system produced a war that nobody wanted.
The difference with cyber: in 1914, mobilization took weeks. In 2026, an exploit chain triggers in minutes.
What this changes
For a European cybersecurity leader, what's happening in Washington might seem distant. It isn't.
Europe built its vulnerability management ecosystem on the American model. NVD as reference, CVE as standard, coordinated disclosure as principle. The European EUVD, launched in 2025, transposes this model.
But the American model is splitting. On one side, public infrastructure (NVD, CISA) continues treating vulnerability as a risk to fix. On the other, the offensive apparatus treats vulnerability as an asset to exploit.
The two cannot coexist indefinitely. When the same government funds both fixing flaws and exploiting them, priorities eventually conflict. The Atlantic Council report says it without phrasing it that way: American Big Tech investing in defense "obstructs" offensive capabilities. To patch is to destroy stock.
Europe is importing a model that the United States is moving away from. It's building a replica while the original mutates.
The question isn't whether Washington is right or wrong. The question is whether Europe wants to follow this mutation or build something else.
The Atlantic Council report meticulously documents the American offensive pipeline. It never asks the question: and those who don't want to play this game, what do they do?
What I don't know
I'm not claiming that the Atlantic Council deliberately coordinates its recommendations with its donors. The circuit I describe may result from a convergence of interests rather than concerted intention.
I also don't know whether Europe has a viable alternative. Building an autonomous vulnerability ecosystem would take a decade. In the meantime, dependence on the American model persists, even as that model fragments.
This article is part of a series analysing the structural flaws of Western cybersecurity (articles 1-5 in French):
- Article 1 : La vulnérabilité de la gestion des vulnérabilités
- Article 2 : La dépendance européenne aux standards américains
- Article 3 : Les États, architectes cachés du marché noir des vulnérabilités
- Article 4 : L'IA ou l'effondrement du modèle défensif occidental
- Article 5 : Desert Power — survivre sans l'Empire
- Article 6: I Am Altering the Deal
- Article 7: The Last Channel
- Article 8: Lord of Cyber War
References
¹ DeSombre Bernsen, W. (2025). "Crash (exploit) and burn", Atlantic Council, Cyber Statecraft Initiative, June 2025 https://www.atlanticcouncil.org/in-depth-research-reports/report/crash-exploit-and-burn/
² Atlantic Council, "Honor Roll of Contributors 2022-2024" https://www.atlanticcouncil.org/support-the-council/honor-roll-of-contributors/
³ Responsible Statecraft (2023). "Weapons firms, donors tied to industry-friendly Atlantic Council report", July 2023 https://responsiblestatecraft.org/atlantic-council-defense-industry/
⁴ Recorded Future (2018). "China's CNNVD Vulnerability Database" https://www.recordedfuture.com/china-vulnerability-disclosure-cnnvd
⁵ CAC/MIIT (2021). Regulation on Management of Security Vulnerabilities (RMSV), September 2021
⁶ See article 3 of this series: "States as hidden architects of the vulnerability black market"