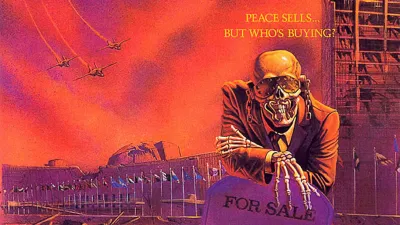
Soylent Green

What defense is made of
The CISO radar analysis ended with a question: why does the system persist when it cannot work? I found some answers. They're public, documented, accessible. The information exists. We choose not to look at it.
The Gartner circuit
Gartner publishes its Magic Quadrants. CISOs consult them. The "Leaders" capture most of the budgets. Companies wanting to appear in the quadrant pay Gartner to be listed, then to improve their position.
Gartner acknowledged this in a 2009 lawsuit: analysts know which vendors pay and which don't¹. The circuit loops: vendors fund Gartner, Gartner defines categories, categories drive purchasing, purchasing funds vendors. If you're not in the loop, you don't count.
Where the Leaders come from
I analyzed the profiles of executives at major cybersecurity companies over twenty years². The data is public.
In the Israeli ecosystem, 80% of founders come from military intelligence, primarily Unit 8200³. Nearly 50% of acquisitions over $100 million involve companies founded by veterans of this unit⁴.
In the American ecosystem, the pattern converges. Leading companies massively recruit former FBI, NSA, and military intelligence officials. The CIA's venture fund, In-Q-Tel, has funded several actors that became major players⁵.
The logic is compelling: offensive expertise naturally transfers to the defensive market. The United States and Israel have built institutionalized pipelines between their agencies and their cyber industry. This symbiosis produces global champions.
Europe has nothing comparable.
100 million events per day
I've already detailed what our organizations transmit to these platforms⁶: 100 million events per day, complete operational mapping, real-time vulnerabilities, business relationship graphs. A handful of actors controlling 70% of the market aggregates this global intelligence.
The nature of this relationship deserves attention.
Two groups in twenty years
I looked for state-sponsored threat groups (APTs) publicly documented by the cyber industry.
The industry abundantly documents Chinese, Russian, Iranian, North Korean APTs. Dozens of groups, thousands of reports, detailed nomenclatures. Five Eyes side: two groups in twenty years⁷.
Equation Group (NSA) was documented by Kaspersky⁸. The Russian vendor was subsequently banned from US government systems⁹.
Two interpretations: either the Five Eyes are extraordinarily discreet, or some vendors detect but don't publish. I don't know which is true. I know the asymmetry raises a question.
When defense "obstructs"
The Atlantic Council documented the American position: vulnerability fixes "obstruct" offensive capabilities¹⁰. The same ecosystem that produces defensive tools considers that defense too effective is a problem.
This aligns with their interests. It only becomes a problem if we forget that our interests may diverge.
Three questions never asked
Three questions appear in no Magic Quadrant, no RFP, no vendor assessment.
First: would my EDR detect an operation by an allied service targeting my organization? Second: would my SIEM alert if a strategic partner exfiltrated data from my systems? Third: does my threat intelligence cover the offensive capabilities of my own security vendors?
Filtered innovation
The radar defines categories. CISOs think within these categories. What isn't listed doesn't exist in budget conversations.
A European startup with an innovative approach, a real idea, a different angle, hits a wall. If it doesn't fit into a Magic Quadrant box, it's invisible. Buyers don't know how to evaluate it. RFPs are calibrated to existing categories. Innovation that doesn't look like what Gartner has already named finds no market.
The circuit filters purchases. It also filters ideas.
More deeply: the radar dispenses with thinking. "What is my security strategy?" becomes "Where am I on the radar?".
A security strategy should start from the business. What does my organization do? What are its critical assets? What specific threats does it face? The answer varies depending on whether you're a hospital, an energy company, a bank, or a defense subcontractor.
The radar proposes the opposite: a universal model to conform to. The strategic question fades behind compliance with the model.
The matrix
The CISO radar says: follow the Leaders, buy certified solutions, align your budgets with defined categories. It doesn't say: verify where these solutions come from, ask yourself why they detect certain threats and not others.
Following the radar without asking these questions means outsourcing your strategic thinking. It means accepting a defense whose priorities and blind spots we don't control.
The radar cannot work as promised. Its real function lies elsewhere: directing purchases toward an ecosystem that thinks cybersecurity for us. Regaining control of our security first requires regaining control of our thinking.
Soylent Green is people.
What I don't know
I'm not claiming a conspiracy exists. The data I present is public. Interpretation remains open.
Companies founded by former intelligence officers can be perfectly legitimate. Expertise acquired in agencies naturally transfers to the private sector. The fact that a founder served in an intelligence unit doesn't prove they continue serving state interests.
I don't know if vendors detect certain operations without publishing them, or if they don't detect them. I don't know if the asymmetry reflects a difference in capability or a difference in willingness.
What I know: as long as we follow a radar without understanding who designed it and why, we don't have a strategy. We have a shopping list.
Eleventh article in a series on the structural flaws of Western cybersecurity (articles 1-5 in French):
- Article 1 : La vulnérabilité de la gestion des vulnérabilités
- Article 2 : La dépendance européenne aux standards américains
- Article 3 : Les États, architectes cachés du marché noir des vulnérabilités
- Article 4 : L'IA ou l'effondrement du modèle défensif occidental
- Article 5 : Desert Power — survivre sans l'Empire
- Article 6: I Am Altering the Deal
- Article 7: The Last Channel
- Article 8: Lord of Cyber War
- Article 9: The digital hawks
- Article 10: They Live... we sleep
References
¹ ZL Technologies, Inc. v. Gartner, Inc. (2009), Case No. 09-CV-01113 EMC, U.S. District Court, Northern District of California — Testimony on analyst awareness of vendor payment status. https://casetext.com/case/zl-technologies-inc-v-gartner-inc
² Analysis based on public sources: LinkedIn, press releases, SEC filings, official company biographies.
³ Rest of World (2022). "Israel's military has intelligence Unit 8200. Gaza has its own version" https://restofworld.org/2022/israel-military-unit-8200-tech/ ; Forbes Israel (2019). "How Unit 8200 Became The Ultimate Startup Machine" https://forbes.co.il/e/how-unit-8200-became-the-ultimate-startup-machine/
⁴ Calcali Tech (2018). "Unit 8200 Alumni Lead Half of Israel's Largest Cyber Acquisitions" — Analysis of acquisitions over $100M. https://www.calcalistech.com/ctech/articles/0,7340,L-3749813,00.html
⁵ In-Q-Tel, public annual reports. The fund has invested in several companies that became major cybersecurity and data analytics players. https://www.iqt.org/
⁶ Franck Rouxel (2024). "The Invisible AI: The Paradox of Modern Cybersecurity" — Analysis of organizational intelligence externalization to EDR platforms. https://www.klaerenn.fr/lia-invisible-le-paradoxe-de-la-cybersecurite-moderne/
⁷ Equation Group (NSA) and Regin (GCHQ) are the only two Five Eyes groups publicly documented. The vast majority of industry APT reports concern Chinese, Russian, Iranian, or North Korean actors.
⁸ Kaspersky Lab (2015). "Equation Group: Questions and Answers" — Technical report documenting Equation Group and its presumed NSA links. https://securelist.com/equation-group-questions-and-answers/68877/
⁹ U.S. Department of Homeland Security (2017). Binding Operational Directive 17-01: prohibition of Kaspersky products in federal agencies. https://www.cisa.gov/news-events/directives/bod-17-01-removal-kaspersky-branded-products
¹⁰ Atlantic Council (2024). "Sleight of Hand: How China Weaponizes Software Vulnerabilities" — Quote: "Apple and Google's privacy and encryption policies [...] obstruct government intelligence-gathering efforts". https://www.atlanticcouncil.org/in-depth-research-reports/report/sleight-of-hand-how-china-weaponizes-software-vulnerability/